Secure AI Agents with CyberArk: A Practical Guide
Learn to secure AI agents with CyberArk for secrets management, access control, and auditable workflows. This guide covers integration and governance for resilient agentic AI deployments.
This guide shows developers and product teams how to secure AI agents using CyberArk for secrets management, access control, and auditable workflows. You will learn integration steps, governance considerations, and practical best practices to reduce risk in agent orchestration. By the end you’ll have a reusable security blueprint for agentic AI in production.
What is CyberArk and why it matters for AI agents
In modern AI environments, credentials travel across multiple services, from cloud APIs to model hosting platforms. The phrase secure ai agents cyberark captures the core idea: keep secrets in a dedicated vault and grant just-in-time access to code and agents. CyberArk provides a centralized vault, policy-driven access controls, and robust auditing that makes it practical to secure agentized workloads without embedding secrets in code. When agents spawn, request, or rotate credentials, a trusted secrets manager acts as the control plane. For enterprise teams, this means fewer blind spots, better compliance, and a clearer path to secure agent orchestration. This approach reduces the attack surface and increases traceability, which is critical as agentic AI workflows scale across distributed environments. The Ai Agent Ops team notes that adopting CyberArk-based secrets management reduces the blast radius of credential exposure and accelerates safe experimentation by decoupling secrets from the agent logic. In practice, you start by mapping what credentials your AI agents need and where those credentials live, then plug CyberArk into the access flow so secret retrieval happens under strict policy. This fosters a culture of secure by default in every agent deployment.
Key security challenges in AI agent ecosystems
AI agents operate at the intersection of software, data, and infrastructure. Without proper controls, secrets drift, credentials outlive their purpose, and a single misconfiguration can cascade across multiple services. A common pattern is embedding API keys in agent code or config files, which becomes a hard-to-detect bug when code migrates between environments. This risk is amplified in multi-tenant or cloud-native environments where different agents share resources. Another challenge is the management of ephemeral credentials and rotation schedules; too long-lived tokens create windows of opportunity for abuse, while overly strict rotation can break automation. Supply chain risk is also real: agents depend on third-party libraries, modules, or connectors that may carry secrets or permissions. Finally, auditing and visibility gaps mean teams cannot reconstruct who accessed what, when, and why. This is where a robust secrets management strategy—anchored by a solution like CyberArk—becomes essential. According to Ai Agent Ops, a defensible agentic AI program requires not only secure storage but also policy-driven access control, consistent rotation, and end-to-end visibility across all orchestration layers.
How CyberArk integrates with AI agents
CyberArk integrates with AI agents by providing a centralized vault for secrets, a policy engine for access control, and the ability to issue dynamic credentials. Agents retrieve credentials on demand through secure channels, never hard-coded in code or configuration. This approach supports least-privilege access, automated rotation, and strong auditing. Organizations can design per-agent or per-workload policies that limit which services a given agent can access and for how long. The result is a more resilient security posture with better traceability across the lifecycle of an agent—from initiation to retirement. Ai Agent Ops highlights that integrating CyberArk into agent orchestration simplifies compliance with regulatory requirements while maintaining development velocity.
Designing an auditable workflow for agent orchestration
Auditing is the backbone of secure AI agent operations. A well-designed workflow records who accessed which credential, when, and for what purpose. Centralized secrets storage makes it easier to correlate access events with agent actions, enabling rapid incident response and deep forensics when anomalies arise. To maximize value, teams should adopt immutable logging, time-bound access tokens, and automated alerts for unapproved access attempts. Integrating CyberArk with your observability stack ensures that access events feed into SIEMs and SOAR platforms, enabling automated containment if a credential is compromised. By establishing a verifiable chain of custody for credentials, organizations can demonstrate governance to stakeholders and regulators. The Ai Agent Ops team recommends keeping access decisions human-in-the-loop for high-risk actions while enabling automated approvals for routine, low-risk secret retrievals.
Practical integration steps
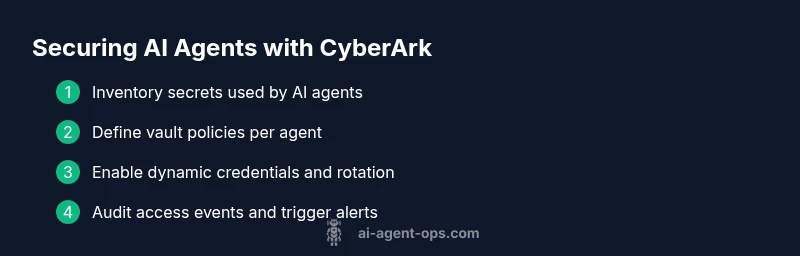
This section offers concrete guidance for putting CyberArk into an AI agent workflow. Start by inventorying secrets used by agents and mapping their access paths. Then configure vaults, rotation policies, and access rules that align with your least-privilege strategy. Next, modify agent code to fetch credentials at runtime via secure channels rather than embedding them. Finally, enable auditing, alerting, and periodic reviews to ensure ongoing compliance. Throughout, maintain separate environments for development, staging, and production to minimize blast radius during upgrades or incident responses. The practical outcome is a robust, auditable pipeline where secrets never leave CyberArk’s control unless strictly authorized and time-bound.
Governance and compliance considerations
Governance for secure AI agents requires explicit policies, role-based access control, and documented procedures for incident response. Organizations should align with industry frameworks (e.g., NIST, ISO) and maintain evidence of controls such as rotation schedules, access reviews, and secure deployment practices. Regular audits and independent penetration testing help verify that the CyberArk integration remains resilient against evolving threats. Ai Agent Ops emphasizes that governance isn’t a one-off task; it’s an ongoing discipline that scales with your agent ecosystem as you add new data sources, services, and deployment regions.
Best practices and pitfalls
Adopt a least-privilege model, enforce automatic secret rotation, and avoid embedding credentials in code or logs. Use per-agent or per-service identity to minimize blast radius, and ensure that credentials are non-persistent beyond need. A common pitfall is treating secrets management as a one-time setup rather than a continuous program; sustain it with periodic reviews and automation. Another mistake is insufficient monitoring—without robust alerts and anomaly detection, a breach can go unnoticed for too long. Finally, always validate integration changes in a staging environment before production rollout to prevent service disruption and data exposure.
Real-world patterns and case studies overview
In practice, teams implement CyberArk-based secret management across AI agent platforms by standardizing secret types, access paths, and rotation lifecycles. Common patterns include per-tenant vault separation, dynamic credentials for database and cloud APIs, and centralized logging for all secret retrieval events. While specific deployments vary by organization, the overarching goal remains the same: reduce the risk surface by removing hard-coded secrets and introducing end-to-end visibility. Ai Agent Ops observations indicate that mature organizations treat secrets management as a programmable capability, enabling automated audits, compliance reporting, and safer experimentation with agentic AI workflows.
Future-proofing secure ai agents cyberark
As AI agents become more capable and integrated into complex business processes, security needs to scale correspondingly. Future-proofing involves adopting scalable policy models, modular integration patterns, and platform-agnostic credential retrieval. Consider layering security controls so that a physical or cloud breach does not grant broad access to vendor APIs or data stores. Regularly review and refresh role definitions, rotate cryptographic keys, and keep up with evolving CyberArk features. By planning for change and investing in automation, enterprises can maintain strong security while accelerating AI-driven innovation.
Tools & Materials
- CyberArk Vault or Conjur-compatible secrets manager(Centralized storage and rotation of credentials for AI agents)
- Cloud credentials and API keys inventory(Inventory of all secrets used by agents across environments)
- Secure networking (private links, VPN, or service mesh)(Isolate agent communication with secrets store)
- Auditing and monitoring tooling(Logs and alerts integrated with SIEM/SOAR)
- OIDC/OAuth2 identity provider(Support for short-lived credentials and SSO)
Steps
Estimated time: 45-75 minutes
- 1
Map secrets and access needs
Identify every secret a given AI agent uses, where it resides, and which services it can reach. Create a per-agent secrets map and categorize by sensitivity.
Tip: Start with the most sensitive credentials (admin keys, keys with broad access). - 2
Define vault policies and roles
Create fine-grained policies that allow access only to the secrets needed by each agent, with time-bound tokens where possible.
Tip: Use per-agent identities and avoid shared credentials. - 3
Enable dynamic credentials
Configure the system to issue short-lived credentials on-demand, and rotate them automatically after use.
Tip: Prefer ephemeral credentials over long-lived tokens. - 4
Integrate into agent orchestration
Modify agents to fetch secrets securely at runtime through authenticated calls to the vault, avoiding hard-coded values.
Tip: Test retrieval paths in a staging environment first. - 5
Implement end-to-end auditing
Capture every access event, correlate with agent actions, and feed into your SIEM/SOAR for automation.
Tip: Triage alerts using playbooks to accelerate response. - 6
Validate and roll out
Run comprehensive tests in a staging environment, simulate breach scenarios, and then deploy with a clear rollback plan.
Tip: Keep a rollback window during initial production rollout.
Questions & Answers
What is CyberArk and how does it help secure AI agents?
CyberArk is a secrets management platform that stores, rotates, and enforces access to credentials. For AI agents, it prevents hard-coded secrets, enforces least-privilege access, and provides audit trails for all secret access.
CyberArk stores and rotates secrets for AI agents, preventing hard-coded credentials and enabling traceable access.
Can CyberArk be used with all AI frameworks and runtimes?
Yes, CyberArk can be integrated with a wide range of AI frameworks and runtimes through standard secret retrieval APIs and IAM integrations. The exact method depends on your stack, but the core concepts remain the same.
Most AI stacks can be wired to CyberArk using standard secret fetchers and identity providers.
How long does it take to implement a CyberArk integration for AI agents?
Time varies by complexity, but a baseline integration with inventory, policies, and runtime secret fetchers can take from a few days to a couple of weeks in a typical enterprise environment.
It usually takes several days to a couple of weeks depending on scope and existing infrastructure.
What are common mistakes when securing AI agents with CyberArk?
Common mistakes include incomplete secrets inventories, broad-permission policies, failure to rotate non-critical credentials, and insufficient logging. Regular reviews and automated testing help prevent these issues.
Missing inventories, overly broad access, and weak auditing are frequent pitfalls; automate checks to avoid them.
Is CyberArk necessary for all AI agent deployments?
CyberArk provides strong secrets management, but the necessity depends on risk tolerance, data sensitivity, and regulatory requirements. For high-risk, regulated environments, it is highly recommended.
Not always required, but highly recommended for high-risk or regulated deployments.
Watch Video
Key Takeaways
- Integrate CyberArk for centralized secrets management
- Enforce least-privilege access for agents
- Enable dynamic credentials with automatic rotation
- Maintain end-to-end auditability across agent orchestration